Mason’s Pre-College Cybersecurity student Tyler Schroder, a freshman at Centreville High School in Clifton, Virginia says he has always been a huge fan of all types of technology.
This year Schroder’s passion for cybersecurity paid big dividends when he made a Common Vulnerably Exposure (CVE) discovery that earned him a publication with corporate partner MITRE and a visit to one of Mason’s Digital Forensics & Cyber Analysis classes.
“In mid-February I was working on my computer at home, and attempting to sign into a website,” Schroder says. “A password manager product I use to sign into the website, Abine Blur, has a feature that can send a second-factor request to your cellphone to make sure it’s actually you requesting to sign into the site. My cellphone was elsewhere in the house when I attempted to sign into the website, and rather than going to get my phone I decided first to see if I could find a quick way around the sign in requirement.” What he found was a vulnerability in the product that would expose user data to a hacker without sending the request.
Schroder credits his instructors at Mason for his knowledge of CVEs. He says they were the reason he knew that he had made a CVE-type discovery and what to do next.
Schroder says, “I had recently learned in my Pre-College Cybersecurity Program class (taught by Jay Gala, MS Digital Forensics and Cyber Analysis student at Mason) about the entire disclosure process, to include the proper steps of how to contact the vendor of the affected product, coordinating patches to fix the vulnerability, and eventually requesting a CVE ID.”
Armed with the knowledge about CVEs, Schroder was able to work through the proper channels so that this vulnerability could be fixed. For his work, he earned the opportunity to present his findings to a Mason Digital Forensics class of master’s students.
For Schroder it was an exciting experience and opportunity to share his findings with other like-minded individuals. “But what made it special was the opportunity to present to an audience that was so much more experienced and educated than I was, in a field that I’d like to work in some day.” Tyler has a bright future.
CVE Link: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-7213
Presentation: https://onedrive.live.com/embed?resid=B123CF3DB421F5D8%213239&authkey=%21ABSNTE3SKNhD8pA&em=2&wdAr=1.3333333333333333&Embed=1
Photo Of Tyler Schroder
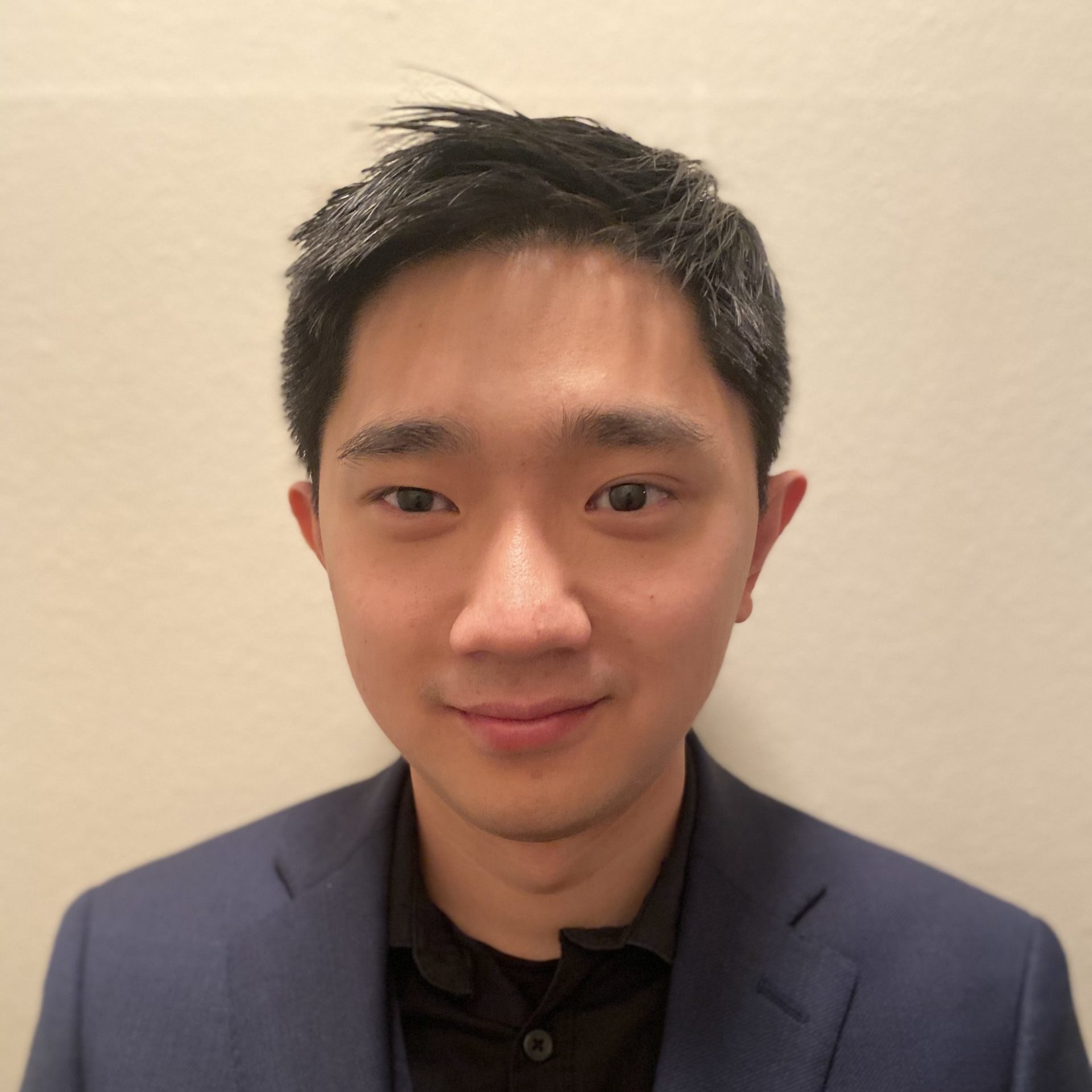
![From Left to Right [Dad, Mom, Tyler Schroder, and Jay Gala (Digital Forensics Mentor)]](https://cfrs.gmu.edu/wp-content/uploads/2019/01/Page-2-Image-1-e1548503092624.jpg)